Strategies to Counteract Online Radicalization
| ✅ Paper Type: Free Essay | ✅ Subject: General Studies |
| ✅ Wordcount: 2946 words | ✅ Published: 04 Sep 2017 |
CHAPTER 2
LITERATURE REVIEW
The purpose of this study is to evaluate existing Bangladeshi efforts to counter radicalization through the internet, identify its weaknesses, and explore opportunities. This research will analyze the significant aspects of successful counter radicalization models of different countries, and suggest ways to incorporate those in Bangladesh to develop a coherent anti-radicalization strategy. Initially, this literature review will discuss the concept of radicalization through the cyberspace. It will allow the readers to follow the subsequent analysis and the suggestions to develop a mechanism in Bangladesh to counter this menace.
The literature review is divided into three sections: understanding online radicalization, online radicalization from a Bangladeshi perspective, and significant aspects of successful international anti-radicalization programs. Understanding online radicalization will examine the potential power of the internet to influence people and the process of radicalization. The section on online radicalization from a Bangladeshi perspective will at first, briefly assess the relevant threats in Bangladesh and will then, identify and evaluate the existing programs of countering online radicalization. The final section will study the strategies adopted by Federal Bureau of Investigation (FBI), The U.S. National Counterterrorism Center (NCTC), and the current programs undertaken by Malaysia and Indonesia. These two countries of Southeast Asia have been selected due to religious and cultural similarities, and geographic proximity. Their programs appear to be effective against online radicalization.
Understanding Online Radicalization
The internet appears to create more opportunities to become radicalized. Many scholarly articles ascribe a role to the internet in promoting radicalization[1]. Those studies suggest that the internet acts as an accelerant, and has broken the traditional barriers to radicalize individuals[2]. In this regard, Gabriel Weimann’s “Terror on the Internet: The New Arena, The New Challenges” counts the number of websites of terrorist groups and reviews their contents[3]. In his article, Weimann points to the proliferation of extremists’ web sites. He founds, by the end of 1999, almost all terrorist groups established their online presence. Different empirical studies suggest, there is a correlation between extremists’ web sites and online propaganda, and rapid radicalization.
The internet enables the terrorists to reach otherwise unreachable individuals. The reach of the internet has blurred the geographic barriers, and connected the distant individuals in the virtual world. Peter Neumann in his research points that the internet allows the terrorists to reach those individuals who would not have been accessible in any other way[4]. For example, Anwar al-Awlaki[5] successfully created online contents such as “Inspire” that advocates ‘jihad from home.’ Ines von Behr asserts, these kind of online materials have broaden the scope to reach any people, and their appealing contents create more chance to implant radical ideas among the individuals[6].
The internet creates opportunities to radicalize a wider range of people from all societies. Rachel and Strugnell identify, beside removing the geographic barrier, the internet has erased the social and gender barriers as well to spread extremist ideologies. They highlight on the internet created scope to reach and radicalize the women[7]. In many societies, it may be difficult for women to meet personally with male extremists or work with them; it may also be difficult for the women to express certain thoughts in public. However, the internet allows them greater anonymity[8]. Some authors opine, the internet benefits the introvert individuals who are seeking the radical ideas by creating a scope to access any content privately[9]. Jerome Bjelopera says, the characteristics of the internet allows a relative advantage to the terrorists in the present days than their previous generations by fading the lines between countries, societies, and genders[10]. The internet provides supposed anonymity and a degree of protection and security from detection[11].
The internet accelerates the process of radicalization. Bjelopera terms the internet as an ‘echo chamber’[12]. It means, people who are searching any radical ideas to support their sketchy thoughts are likely to get some reinforcing contents on the internet due to its massive storage. The internet is a kind of ‘one-stop shop’ for all the information that an individual may seek to underline his radical ideas that expedites his radicalization process. The virtual world reduces the timeframe of radicalization process as opposed to the actual world. Anthony Bergin in his study refers the internet as a “conveyor belt” that accelerates the radicalization process by providing instantaneous and continuous connection to any violent idea[13]. Raffaello Pantucci further highlights the internet’s role in incubating and accelerating radicalization[14]. Robert Schmidle points that, the chat rooms in particular are effective for the extremists since they can exchange ideas with like-minded individuals 24/7 regardless of borders[15]. Therefore, the internet expedites the radicalization process of any individual by offering varieties of contents and continuous interaction.
The internet allows radicalization to occur without physical contact. Yeap and Park explain, the internet enables any individual to access radical contents from their personal space instead of attending a radical religious gathering[16]. Therefore, an individual need only the internet connection, physical travelling to other location is no more essential. Though the internet reduces hurdles to interaction, few scholars may argue that human interaction is necessary for radicalization. However, Behr says, in a digital era the ‘online’ activities may be considered as an extension of the real lives, and physical connection is no more essential[17]. Beside the actual world, personal relationship may grow in the virtual world as well. Thus, Mitchell Silber and Arvin Bhatt asserts, “radicalization on the internet is not necessarily any different to what would happen with other more private and less visible sources[18].” Besides, the internet increases opportunities for self-radicalization. It is a process where an individual gradually become radicalized by himself [19]. Hence, the internet creates opportunities of radicalization without human interaction.
An individual move through several phases as he becomes radicalized through the cyberspace. In a New York Police Department radicalization case study, Silber and Bhatt identify four phases of radicalization: pre-radicalization, self-identification, indoctrination and jihadization[20]. The case study recognizes the impact of the internet on the radicalization process as an individual looking for “an identity and a cause”[21]. The internet facilitates in each of the stages to instruct, socialize, indoctrinate and recruit[22]. The FBI has also created a radicalization model similar to that of the NYPD. The FBI model has four stages: pre-radicalization, identification, indoctrination and action[23]. These categories are almost similar to NYPD. The diagram below illustrates the Moghaddam’s staircase to radicalization where the online contents play a complementary role:
Moghaddam Staircase to Radicalization
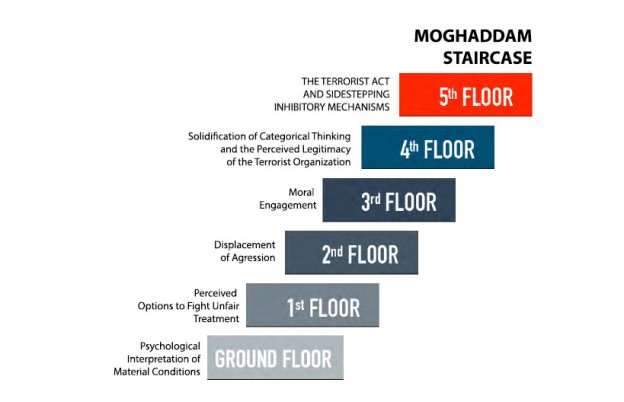
Source: Moghaddam, Fathali M. The Staircase to Terrorism, A Psychological Exploration, Vol. 60, No. 2, American Psychologist, 2005.
Online Radicalization in Bangladeshi Perspective
Terrorists’ Approach and their Target Audience
In Bangladesh, few religion based terrorist organizations have gained capabilities to develop and spread their radical messages online. They have attracted public and media attention through their activities and propagation. Besides, few leftist political groups are also trying to develop their online capabilities. At present 13 terrorist organizations are operating actively and 29 others are operating covertly using fake credentials[24]. The Special Branch of Bangladesh Police has provided the names of eight terrorist organizations to Home Ministry who are very active on the internet: Ansarullah Bangla Team, Allah’r Dal, Islamic Solidarity Front, Tamiruddin Bangladesh, Tawhidee Trust, Hizbut-Tawhid, Shahdat-e-Nabuwat and Jamat-as-Sadat. Five of these terrorist organizations have already been banned by the government, and eight more are yet to be banned[25]. These groups may have significant investment, both human and financial, to build their online capacities.
The terrorist groups of Bangladesh appear to be active on the internet, particularly in Facebook and YouTube, to spread radical preaching. This is safer, and lower possibility of being tracked by the law enforcing agencies. Farooq opines, the online propaganda of the terrorists in Bangladesh have become more organized, and appealing to their targets[26]. Arman claims that the terrorists try to exploit the ethno-religious sentiment of the people while developing their messages, and appeal to their believes to embed their radical ideas[27]. Over the last few years, hate speeches and violent ideologies that spread through the internet triggered a number of terrorist attacks and communal violence in Bangladesh. This was evident in Ramu and Pabna incidents where mass attacks were carried out on religious minority people. In both cases, unidentified persons using pseudonyms posted doctored photos and messages on the Facebook defaming Islam that agitated people[28]. Social media have become the easiest means to spread radical ideas in Bangladesh.
Bangladeshi youths are particularly vulnerable to online radicalization due to lack of cyber awareness. Farooq in his study opines, the terrorists seem to target the educated youths by spreading appealing messages on the Internet[29]. It is easier to radicalize the youths than the elders since they are more connected to the online world. Farooq also opines, many Bangladeshi youths at first just curiously run across radical contents, and gradually fall into the traps unconsciously. The concept of cyber awareness and related programs seem insufficient in Bangladesh. As a result, neither the youths nor their parents or guardians are aware about the online traps. Immediately after the terrorist attack at the Holey Artisan Bakery restaurant, RAB released a list of 261 missing youths across the country[30]. These missing youths are suspected to have joined various terrorist groups.
The terrorists in Bangladesh attempt to build their radical narratives based on religious and socio-political contentious issues. Nirmal Ghosh opines, though Bangladesh is politically a secular country, the terrorist appeal to the Muslim majority population to make it an Islamic state under Sariah law[31]. They seem to exploit the religious sentiment of the people. These groups intentionally create fake photos with radical messages such as prosecution of Muslim Rohingyas and spread those on social media to instill communal violence in the country[32]. Furthermore, the extremists adeptly construct radical narratives on socio-economic disparity and political issues to create sympathizers.
Bangladeshi Counter Radicalization Programs
The Bangladesh government has implemented several plans and strategies to counter radicalization in the country. However, Abul Kalam argues that, the government has mostly implemented coercive approaches to minimize the terrorist threats[33]. Aynul Islam in his article, categorizes the government initiatives into two types: operational drives by the law and security forces, and legal initiatives[34]. The law enforcement agencies have achieved some success in disrupting few of the extremist groups. Many extremist leaders and activists have been arrested, put under trial. However, the terrorists’ online activities apparently remain undisrupted due to lack of government action. The National Monitoring Cell (NMC) monitors the suspicious online activities, but it has limited capacity and expert workforce. The government effort to shut down or censor few websites seem not very effective, because extremists innovate new ways to reach people. Moreover, it is difficult to identify and stop secret groups in social networking sites that contains radical ideas.
Bangladesh government has enacted a few legislations to ensure the cyber security. Bangladesh Telecommunication Regulatory Act 2001, The ICT Act 2006, Digital Security Act 2016 (Draft) are at present the main legislations of Bangladesh to enforce cyber security. On 11 June 2008, the Anti-Terrorism Ordinance 2008 was approved by the government, and was amended in 2013[35]. The new counter terrorism legislation has kept maximum punishment – a death sentence – for terrorist activities. However, in most cases the laws have not been enforced against persons who carry out propaganda in the cyberspace.
Bangladesh has number of agencies with counterterrorism cells. Islam opines, capabilities and activities of these agencies are not orchestrated[36]. Their roles are not specified, and efforts are fragmented. The Bangladesh Police, the Rapid Action Battalion (RAB), Bangladesh Rifles (BDR), armed forces and intelligence agencies are mainly responsible for fighting terrorism. All of these forces have counter terrorism cells, but they work separately. He further argues that, the police are not well equipped and trained to deal with the new trends of online terrorism. The intelligence agencies are essential apparatus in support of operational activities. The National Security Intelligence (NSI), the Directorate General of Forces Intelligence (DGFI), Special Branch (SB) of Police and the RAB intelligence wing have been working in Bangladesh to identify the potential threat sources. There is no set mechanism through which the forces can share intelligence and coordinate their collection efforts. In May 2004, NSI constituted a separate body called “counter terrorism cell” to identify specific risk population and areas, and threat groups. The “counter terrorism bureau” of DGFI, has been working to evaluate, analyze, and frame counter terrorism policy at strategic and operational level[37]. Nonetheless, there is no overarching organization to synchronize these wide varieties of organizations in the country[38].
Islam in his article, Mapping Terrorism Threats in Bangladesh, identifies few key deficiencies of Bangladeshi programs to prevent radicalization[39]. First, Bangladesh has no set mechanism to monitor the internet for preventing radical ideas. He opines that there is a lack of knowledge and understanding of the threats that can spread through online. Neither the country has sufficient technological and organizational expertise, nor it has workable international cooperation for capacity building. Second, the law enforcement agencies do not have close link with the other service sectors or private sectors to identify suspicious activities. Third, the Bangladesh government is not sufficiently addressing strategic issues like de-radicalization and counter ideology. Fourth, there is a very limited initiative to educate professional groups like academics, media community, service sector officials, and political leaders to create general awareness. There is almost no community based programs in the country for developing cyber awareness. Fifth, the government overemphasizes coercive approaches in dealing with terrorism issues. There is no dedicated research institution in the government to provide forum for understanding and research on critical issues of terrorism like online radicalization. Although the counter terrorism bureau of DGFI is responsible for policy related activities, it is barely possible to formulate a viable strategy by a body of armed forces alone. Finally, he mentions that, in Bangladesh, strategies and policies are highly bureaucratic, ambiguous, and unaccountable[40].
References
[1] Precht, Tomas. Homegrown Terrorism and Islamist Radicalisation in Europe: From Conversion to Terrorism. An Assessment of the Factors Influencing Violent Islamist Extremism and Suggestions for Counter Radicalisation Measures, Copenhagen: Danish Ministry of Defence, 2008.
[2] Pantucci, Raffaello. A Typology of Lone Wolves: Preliminary Analysis of Lone Islamist Terrorists. Developments in Radicalisation and Political Violence, International Centre for the Study of Radicalisation and Political Violence, 2011.
[3] Weimann, Gabriel. Terror on the Internet: The New Arena, The New Challenges. Washington, DC: United States Institute of Peace Press, 2006.
[4] Neumann, Peter R. Options and Strategies for Countering Online Radicalization in the United States. Studies in Conflict & Terrorism, 2013.
[5] Anwar al-Awlaki was a spokesperson and recruiter for Al Qa’ida.
[6] Ines von Behr, Anaïs Reding, Charlie Edwards, Luke Gribbon. Radicalisation in The Digital Era. RAND Corporation, 2103. 17.
[7] Briggs, Rachel and Alex Strugnell. Radicalisation: The Role of the Internet. Policy Planners’ Network Working Paper, London: Institute for Strategic Dialogue, 2011.
[8] Schmidle, Robert E. Positioning Theory and Terrorist Networks. Journal for the Theory of Social Behaviour, Vol. 40, No. 1, 2009, 65.
[9] Torok, Robyn. Make a Bomb in Your Mums Kitchen: Cyber Recruiting and Socialisation of White Moors and Home Grown Jihadists. Edith Cowan University Research Online, 2010.
[10] Bjelopera, Jerome P. American Jihadist Terrorism: Combating a Complex Threat. Congressional Research Service Report for Congress, Washington, DC: Congress Research Service, 2011, 101-102.
[11] Weimann. Terror on the Internet: The New Arena, The New Challenges.
[12] Bjelopera. American Jihadist Terrorism: Combating a Complex Threat. 101-102.
[13] Bergin, Anthony. Countering Online Radicalisation in Australia. Australian Strategic Policy Institute Forum, 2009.
[14] Pantucci, Raffaello. A Typology of Lone Wolves: Preliminary Analysis of Lone Islamist Terrorists. Developments in Radicalisation and Political Violence, International Centre for the Study of Radicalisation and Political Violence, 2011.
[15] Schmidle, Robert E. Positioning Theory and Terrorist Networks. Journal for the Theory of Social Behaviour, Vol. 40, No. 1, 2009, 65.
[16] Yeap, Su Yin and Jenna Park, ‘Countering Internet Radicalisation: A Holistic Approach’. S. Rajaratnam School of International Studies, 2010. 2.
[17] Ines von Behr, Anaïs Reding, Charlie Edwards, Luke Gribbon. Radicalisation in the Digital Era. RAND Corporation 2013. P.20.
[18] Silber, Mitchell D. and Arvin Bhatt. Radicalization in the West: The Homegrown Threat. New York: New York City Police Department, 2007.
[19] Change Institute. Studies into Violent Radicalisation: Lot 2 – The Beliefs Ideologies and Narratives. 2008.
[20] Silber and Bhatt, Radicalization in the West: The Homegrown Threat. 6-7.
[21] Silber and Bhatt, Radicalization in the West: The Homegrown Threat. 8.
[22] Silber and Bhatt, Radicalization in the West: The Homegrown Threat. 8-9.
[23] Silber and Bhatt, Radicalization in the West: The Homegrown Threat. 30.
[24] Farooq Sobhan. The Role of Civil Society in Countering Radicalization in Bangladesh. Bangladesh Enterprise Institute, Dhaka 2014. P. 8.
[25] Farooq Sobhan. The Role of Civil Society in Countering Radicalization in Bangladesh. Bangladesh Enterprise Institute, Dhaka 2014. P. 8.
[26] Sobhan, Farooq. The Role of Civil Society in Countering Radicalization in Bangladesh. Bangladesh Enterprise Institute, Dhaka 2014. 13.
[27] Tanbir Uddin Arman. New Media, Digital Radicalization and Social Security. The Bangladesh Today, 2015.
[28] Arman. New Media, Digital Radicalization and Social Security. The Bangladesh Today, 2015.
[29] Farooq Sobhan. The Role of Civil Society in Countering Radicalization in Bangladesh. Bangladesh Enterprise Institute, Dhaka 2014. 10.
[30] Bdnews24.com. Web: http://bdnews24.com/bangladesh/2016/07/20/rab-releases-list-of-261-persons-missing-from-across-bangladesh.
http://www.straitstimes.com/opinion/battle-for-bangladeshs-soul-as-islamic-radicals-push-for-power
[32] Tuhin Shubhra Adhikary and Wasim Bin Habib, Fake photos trolling,
http://www.thedailystar.net/frontpage/fake-photos-trolling-1320613
[33] Kalam, Abul. The Challenges of Terrorism: Bangladesh Responses. Moni, SD. (ed) Responding to Terrorism in South Asia, Monohar, New Delhi, 2006.
[34] Islam, Aynul M. Mapping Terrorism Threats in Bangladesh. Bangladesh Institute of International and Strategic Studies, Dhaka, April 2008. P. 165.
[35] The Daily Star, 18 June 2008.
[36] Islam, Aynul M. Mapping Terrorism Threats in Bangladesh. Bangladesh Institute of International and Strategic Studies, Dhaka, April 2008. P. 165.
[37] Hussain, Sakhawat M. Capacity Building of Law Enforcement and Intelligence Agencies. Farooq Sobhan, ed, Counter Terrorism in Bangladesh. University Press Limited, Dhaka, 2008, p. 70.
[38] Islam, Aynul M. Mapping Terrorism Threats in Bangladesh. Bangladesh Institute of International and Strategic Studies, Dhaka, April 2008. P. 165.
[39] Islam, Aynul M. Mapping Terrorism Threats in Bangladesh. Bangladesh Institute of International and Strategic Studies, Dhaka, April 2008. P. 167-168.
[40] Islam, Aynul M. Mapping Terrorism Threats in Bangladesh. Bangladesh Institute of International and Strategic Studies, Dhaka, April 2008. P. 167-168.
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allDMCA / Removal Request
If you are the original writer of this essay and no longer wish to have your work published on UKEssays.com then please click the following link to email our support team:
Request essay removal


